Privileged Access Management software for secure, documented, and efficient remote access to IT/OT infrastructure, supporting compliance and integration.
Vendor
Amitego
Company Website
Amitego provides enterprise-grade software solutions for secure IT access management, specializing in privileged access management (PAM) and remote access security for critical infrastructures. Its flagship product, VISULOX, enables organizations to control, monitor, and document privileged user activities across IT and OT environments without requiring changes to existing servers or clients. The solution is designed for seamless integration, offering agentless deployment and compatibility with heterogeneous infrastructures. VISULOX supports just-in-time access, multi-factor authentication, and session recording, ensuring compliance with regulatory standards and reducing security risks. The platform is suitable for organizations with distributed workforces and complex access requirements, providing robust security, transparency, and operational efficiency.
Key Features
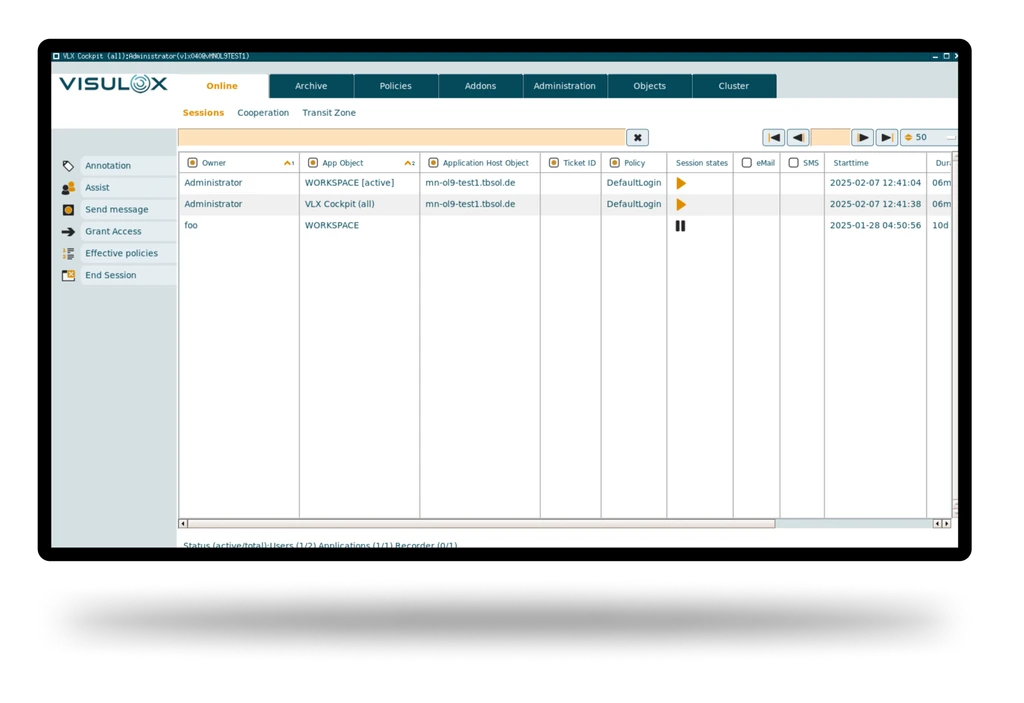
Privileged Access Management (PAM) Centralized control and monitoring of privileged users.
- Manages and restricts access to critical systems and data.
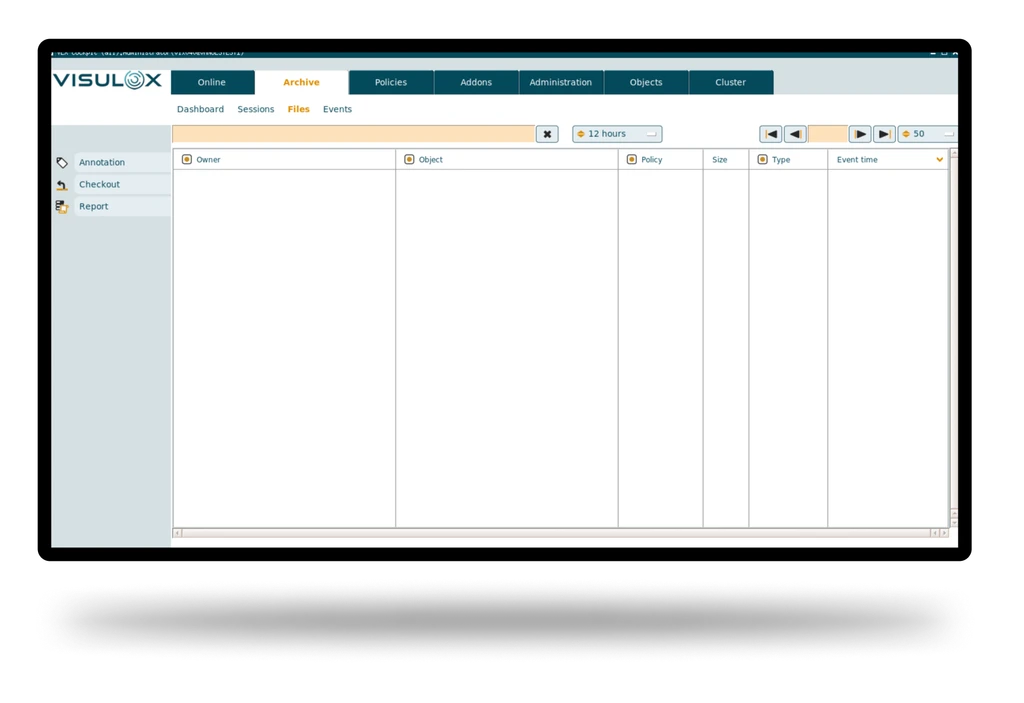
- Provides detailed documentation and audit trails of all privileged activities.
Remote Access Security Secure, seamless remote connections for IT/OT environments.
- Enables secure remote access without infrastructure changes.
- Supports agentless installation for rapid deployment.
Session Recording and Monitoring Comprehensive oversight of user actions.
- Records and monitors all privileged sessions for compliance and forensic analysis.
- Ensures transparency and accountability in user activities.
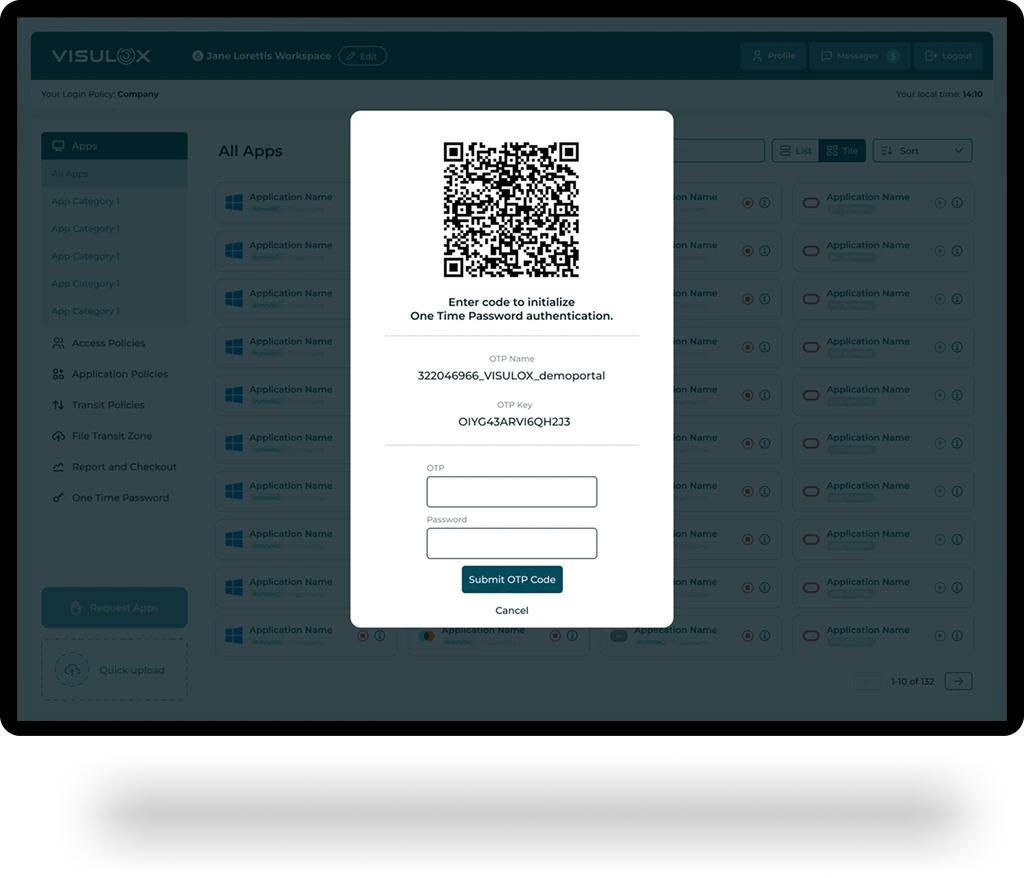
Multi-Factor Authentication Enhanced identity verification.
- Integrates robust authentication mechanisms to prevent unauthorized access.
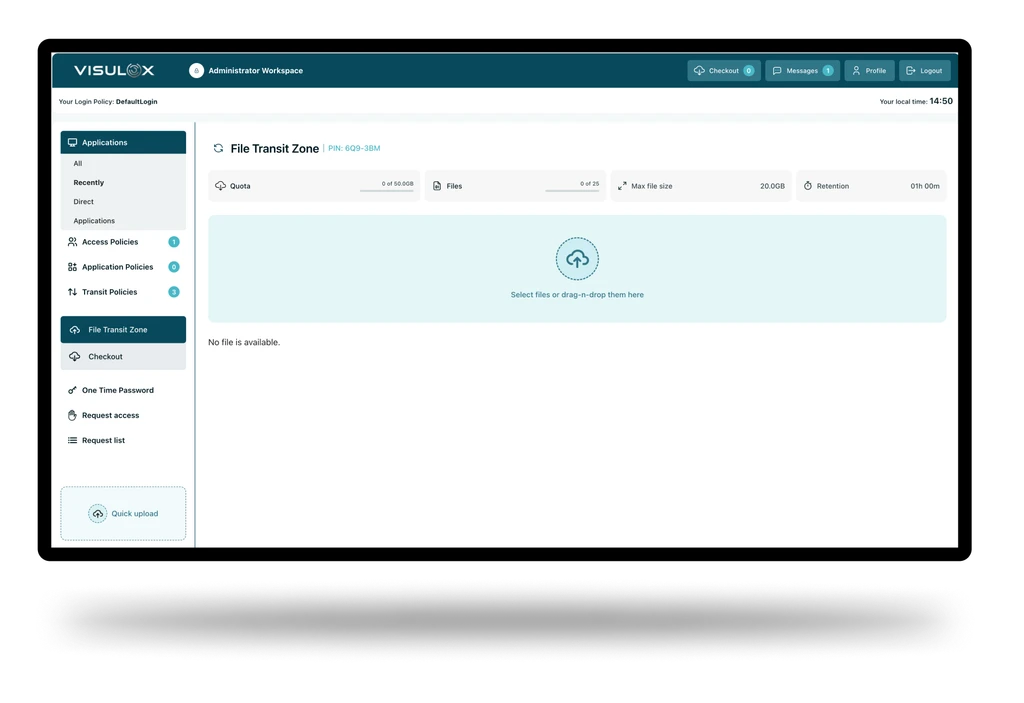
Just-in-Time Access Temporary, controlled access for specific tasks.
- Reduces attack surface by limiting access duration and scope.
Seamless Integration Works with existing infrastructure.
- Compatible with heterogeneous client environments and legacy systems.
- No changes required on servers or clients for deployment.
Benefits
Improved Security and Compliance Protects critical infrastructure and meets regulatory requirements.
- Reduces risk of unauthorized access and data breaches.
- Facilitates compliance with standards through detailed documentation and monitoring.
Operational Efficiency Streamlines access management and reduces administrative overhead.
- Agentless deployment minimizes disruption and accelerates implementation.
- Centralized management simplifies oversight and reporting.
Transparency and Accountability Ensures all privileged activities are tracked and auditable.
- Provides clear audit trails for investigations and compliance audits.