
Secure Your Virtual Machines the Fastest and Easiest Way No Deployment. No Keys. Drop in the Images. Get the Insights.
Vendor
ReversingLabs
Company Website
Overview
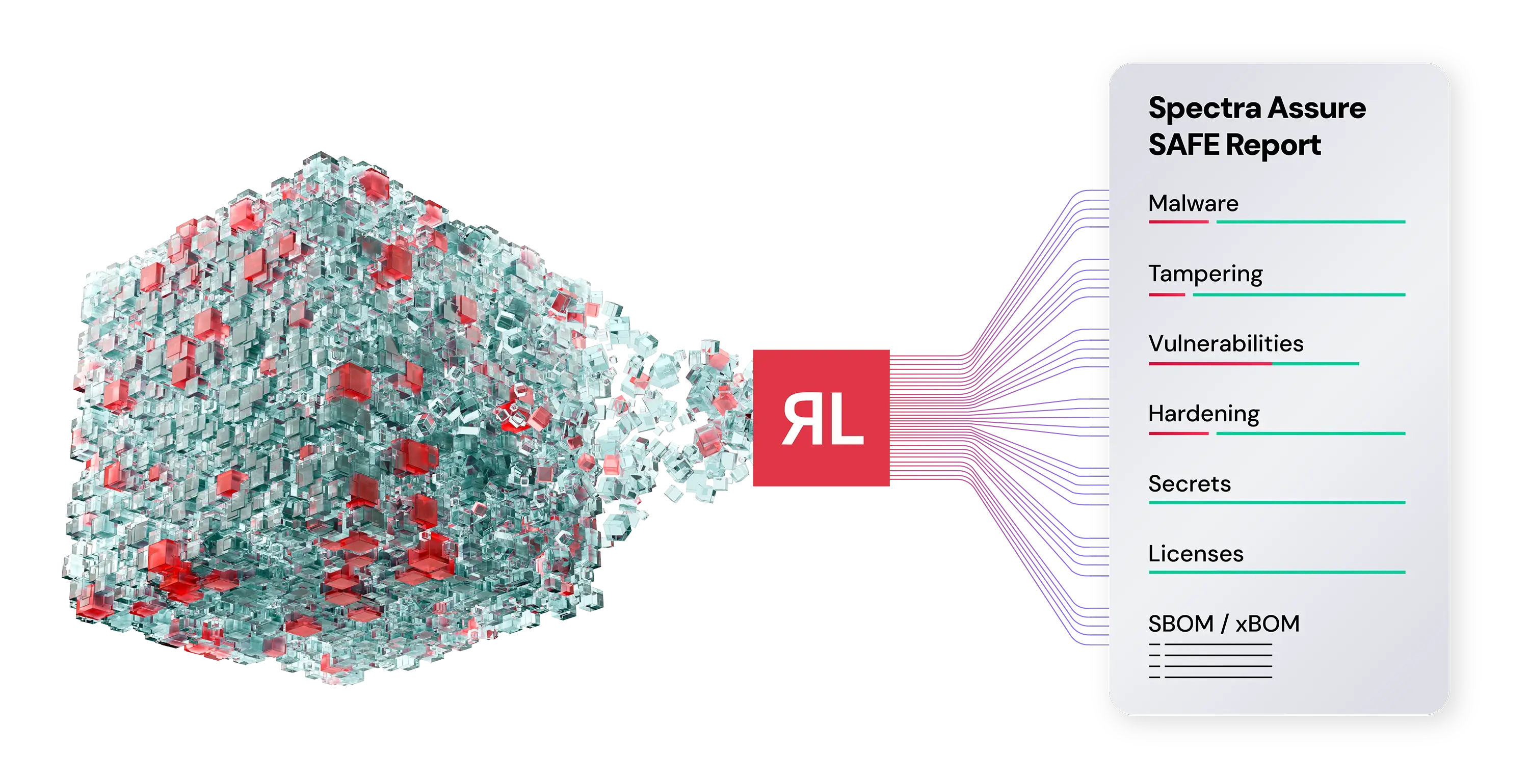
ReversingLabs' Secure Virtual Machine Images solution, part of the Spectra Assure platform, offers a pre-deployment security analysis for virtual machine (VM) disk images. Unlike traditional methods that require VM deployment and runtime access, this solution allows organizations to assess the security of VM images before they are deployed, significantly reducing potential risks and vulnerabilities. By leveraging Spectra Assure's advanced scanning capabilities, users can identify embedded threats, such as malware, exposed secrets, vulnerabilities, and tampered components, without the need for deployment or agent-based monitoring. This approach not only enhances security but also streamlines the deployment process, ensuring that only secure and compliant VM images are utilized in production environments.
Features and Capabilities
- Comprehensive Disk Image Analysis: Supports major VM disk image formats, including VMDK, VHD, VDI, QCOW2, DMG, and OVA, enabling thorough security assessments across diverse environments.
- Large File Support: Capable of analyzing disk images up to 50GB in size, accommodating enterprise-level VM images without compromising performance.
- Pre-Deployment Security Assessment: Eliminates the need for VM deployment by providing a static analysis of disk images, identifying risks before runtime.
- Automated Assessment Workflows: Integrates seamlessly into existing CI/CD pipelines, automating the security validation process and ensuring consistent assessments across the organization.
- Comprehensive Risk Reporting: Generates detailed SAFE reports that highlight identified threats, vulnerabilities, and compliance issues, facilitating informed decision-making and remediation efforts.
- Enhanced Threat Detection: Utilizes advanced threat intelligence and behavioral analysis to detect known and unknown threats, including malware, vulnerabilities, exposed secrets, and tampered components.
- No Runtime Access Required: Operates without the need for VM deployment or agent-based monitoring, simplifying the security assessment process and reducing operational overhead.
- Cross-Platform Compatibility: Supports Windows, Linux, and macOS file systems, ensuring comprehensive security assessments across various operating environments.