
Secure unstructured data and prevent unauthorized access
Vendor
OpenText
Company Website
Overview
OpenText™ Data Access Governance (NetIQ) is a comprehensive solution that pinpoints where valuable files are stored and identifies the individuals who can access them. It then automatically makes necessary adjustments to ensure your unstructured data is secure, optimized, and compliant.
How OpenText Data Access Governance can benefit business
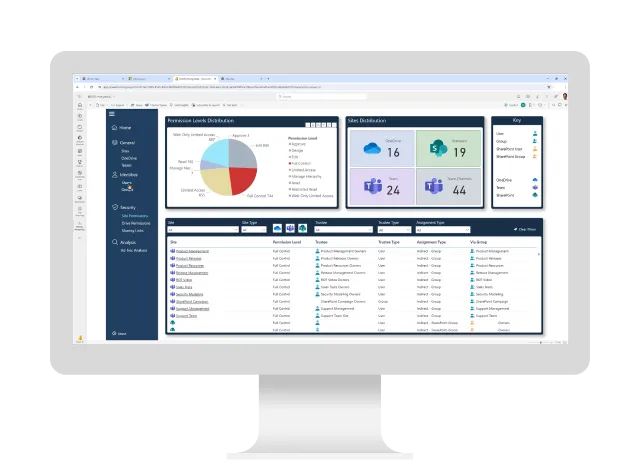
Gain visibility into data access
Analyze file system data to understand what data you have and who has access to it.
Streamline user provisioning
Automatically provision data storage, assign permissions, and control access.
Reduce data access risk
Monitor high-risk data, enforce fencing policies, and notify owners when access permissions change.
Govern data access
Empower business users to certify access to data and applications in the same interface.
Why OpenText Data Access Governance?
Automated actions
Streamline the management of file locations and access rights to reduce manual effort and enhance data governance efficiency.
Fencing and lockdown policies
Protect critical data from unauthorized access by implementing fencing and lockdown policies that ensure only authorized users can access sensitive information.
Sensitive data access control
Meet regulatory requirements by demonstrating strict control over access to confidential and sensitive unstructured data, maintaining compliance and security.
Key features
Enhanced reporting
Enables corrective measures with improved reporting that can identify sensitive and high-value files and track user access.
Least privilege user access
Protects sensitive and high-value data repositories by limiting access permissions only to policy-authorized users—preventing “privilege creep” over time.
Overexposure correction
Identifies unauthorized access to sensitive and high-value data, whether due to improper group membership or insecure storage, and enacts policies or workloads to mitigate the associated risks.