
AI-powered SaaS platform for automated security validation and exposure management, continuously optimizing cyber defenses.
Vendor
Cymulate
Company Website
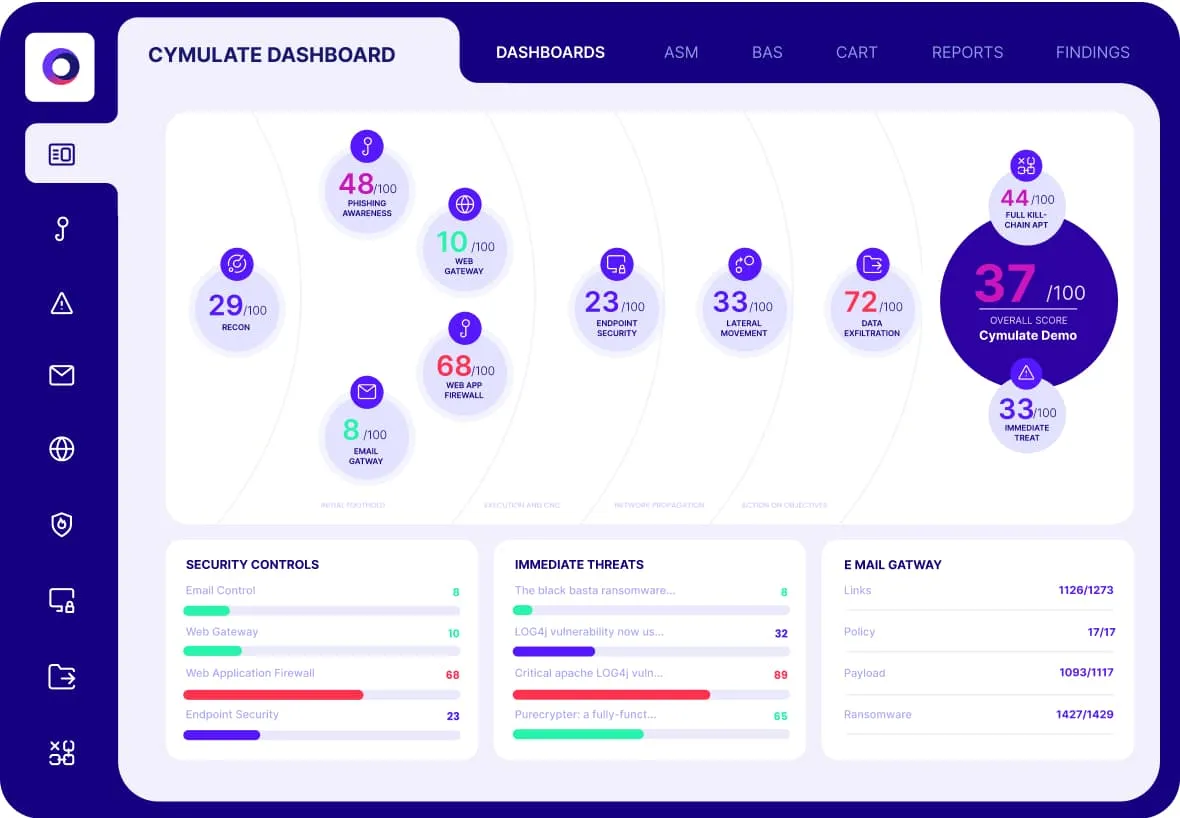
Cymulate is a cloud-based platform that automates security validation by simulating real-world cyberattacks, continuously assessing your security controls, and prioritizing exploitable risks. It provides actionable insights and remediation guidance to help organizations optimize their cyber resilience and reduce threat exposure across on-premises and cloud environments.
Key Features
Automated Security Validation Continuously test and validate security controls using real-world attack simulations.
- Simulates the latest attack techniques and campaigns.
- Identifies gaps in prevention, detection, and response.
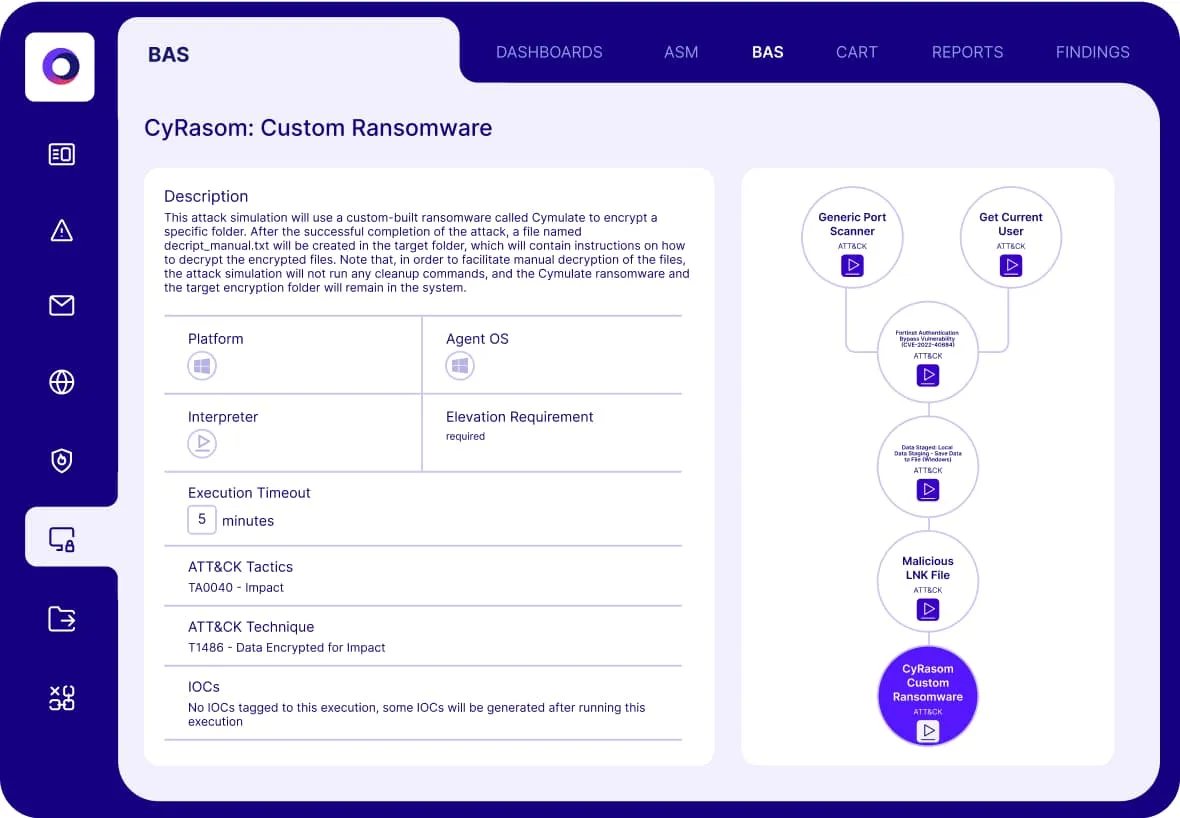
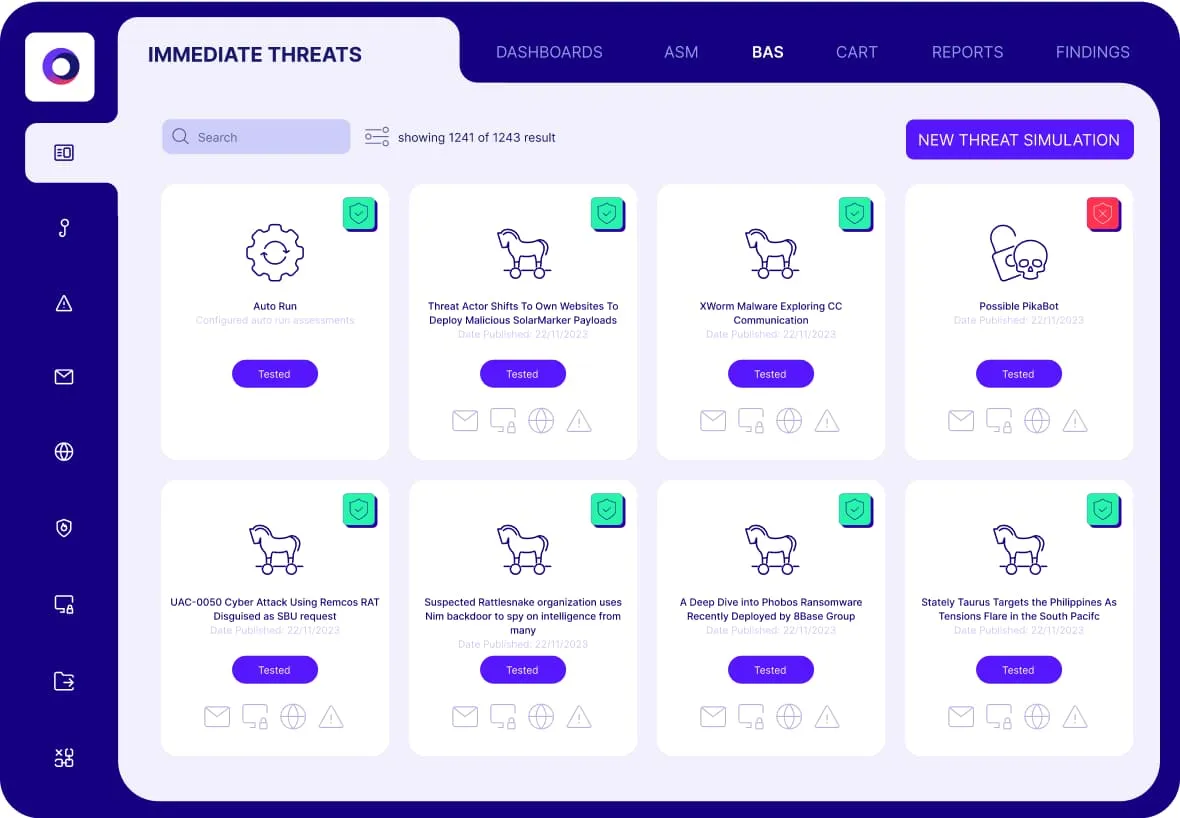
Breach and Attack Simulation (BAS) Emulates adversary behavior to assess security effectiveness.
- Runs automated attack scenarios across endpoints, networks, and cloud.
- Provides templates and daily updates for new threats.
Continuous Automated Red Teaming (CART) Performs advanced, ongoing offensive testing.
- Executes chained attack scenarios for in-depth assessments.
- Validates exploitability of vulnerabilities and exposures.
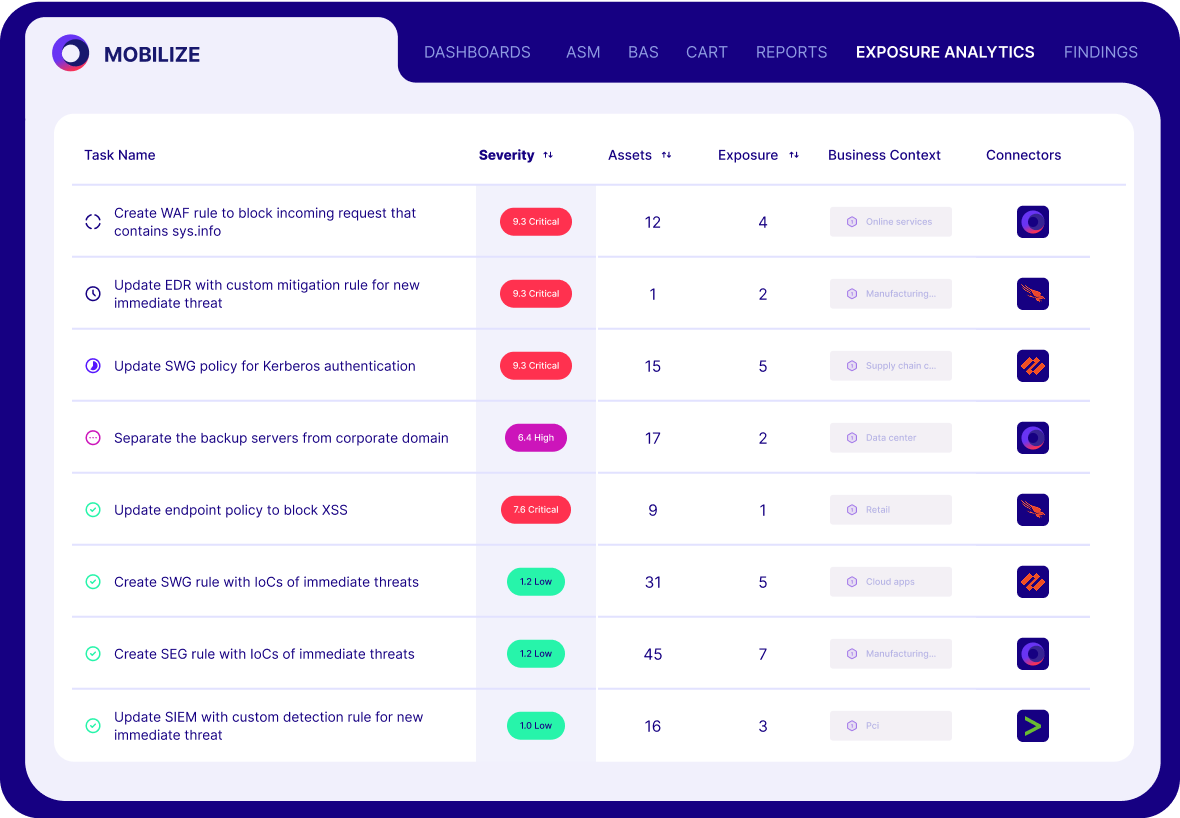
Exposure Analytics Prioritizes threats based on validated, exploitable risks.
- Correlates control effectiveness, threat intelligence, and business context.
- Provides operational metrics, benchmarking, and board-ready reports.
Remediation Guidance Delivers actionable recommendations to close security gaps.
- Suggests configuration updates and custom detection rules.
- Pushes new indicators of compromise (IoCs) to security controls.
AI-Powered Threat Assessment Uses AI to create custom attack scenarios and assessments.
- Converts threat intelligence and advisories into actionable tests.
- Reduces time to value and removes human bias in testing.
Technology Integrations Integrates with existing security tools and IT infrastructure.
- Supports EDR, SIEM, SOAR, vulnerability management, cloud security, and ticketing systems.
- Automates updates and streamlines security operations.
Benefits
Proactive Risk Reduction Continuously identifies and remediates exploitable security gaps.
- Focuses remediation on what attackers can actually exploit.
- Reduces noise by filtering theoretical risks from real exposures.
Operational Efficiency Automates complex testing and reporting processes.
- Increases team efficiency and accelerates threat response.
- Enables both blue and red teams to run and customize assessments easily.
Improved Cyber Resilience Provides measurable, evidence-based security posture.
- Benchmarks resilience against industry frameworks and peers.
- Offers proof of risk reduction for stakeholders and compliance.
Comprehensive Coverage Validates controls, threats, and response across all environments.
- Covers endpoints, networks, cloud, applications, and identities.
- Adapts to evolving threat landscapes with continuous updates.