
ThreatLocker Cyber Hero MDR enhances ThreatLocker Detect with 24/7 managed services, monitoring and responding to Indicators of Compromise. The Cyber Hero Team ensures rapid response to threats, minimizing risks and maintaining security around the clock.
Vendor
ThreatLocker
Company Website
ThreatLocker® Cyber Hero® Managed Detection and Response (MDR)
Unleash the full potential of the ThreatLocker® Detect EDR solution with managed services from the 24/7/365 ThreatLocker Cyber Hero Team.
What is ThreatLocker® Cyber Hero® Managed Detection and Response? (Cyber Hero® MDR)
Cyber Hero® MDR is an add-on to ThreatLocker Detect that allows organizations to opt for the ThreatLocker Cyber Hero Team to monitor and respond to Indicators of Compromise (IoC). When ThreatLocker Detect identifies suspicious activity in your environment, the Cyber Hero Team will review the alert to determine if there is a true IoC or a false positive. In the event of a cyber incident, the Cyber Hero Team will follow the customer's runbook to either isolate or lock down the device and notify the customer. They will be able to identify additional information for the customer, including:
- What the threat was
- How initial access was gained
- Where the threat originated
- What the threat attempted to do
- How the threat was blocked and mitigated
Prompt notifications 24/7/365
The 24/7/365 availability of the ThreatLocker Cyber Hero Team offers around-the-clock Managed Detection and Response (MDR) services to keep organizations secure and alert even outside of standard hours of operation. The Cyber Hero Team has an average response time of 60 seconds. This metric is unique to ThreatLocker and provides a significant advantage when responding to threats. By augmenting the ThreatLocker Zero Trust Endpoint Protection Platform with managed detection and response servers, customers can reduce agent fatigue while hardening their environment to the highest standards, ensuring the mitigation and notification of attempted attacks.
Features
Alerts and detects
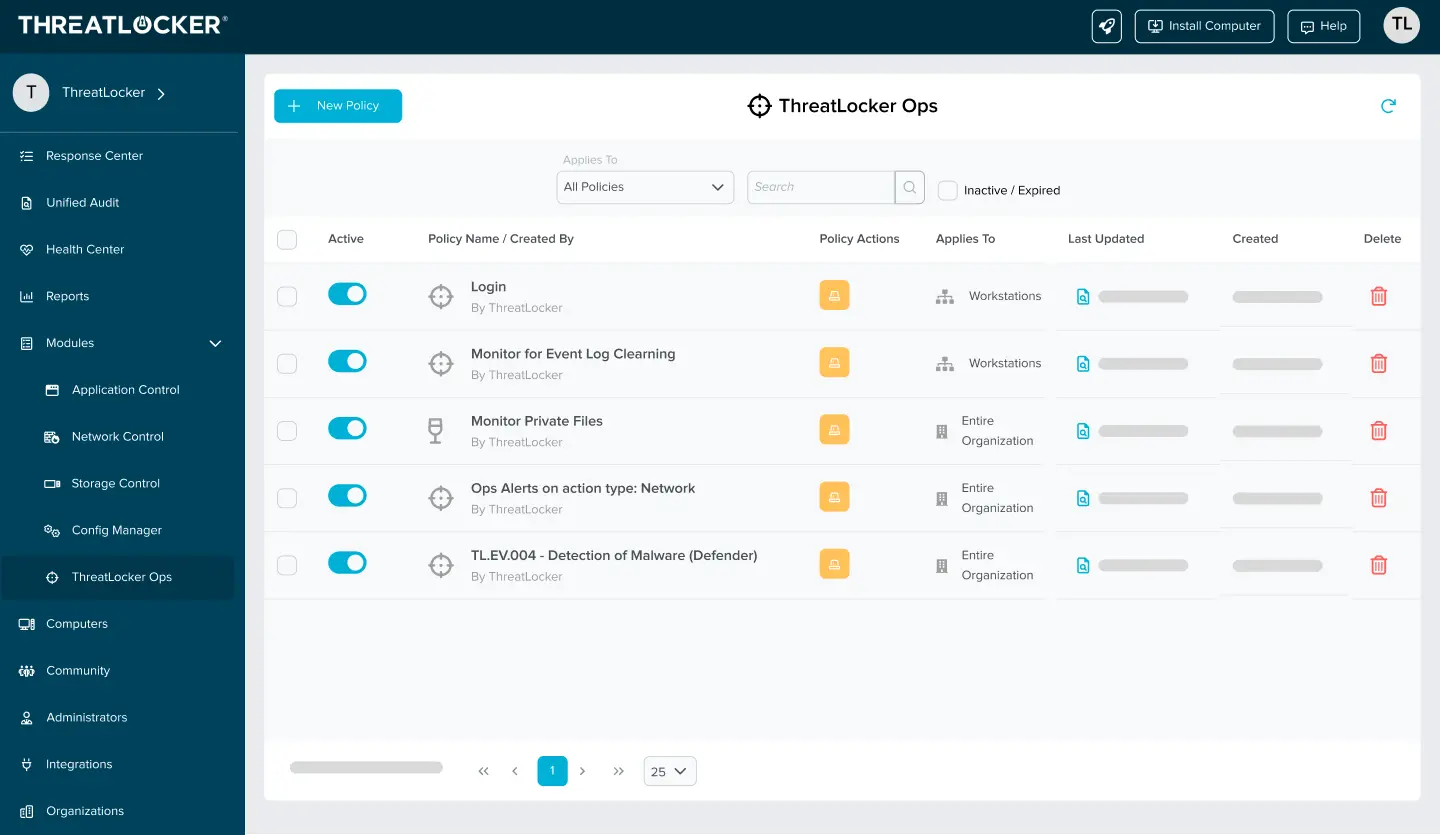
Using industry-known indicators of compromise, ThreatLocker Detect can identify and alert IT professionals that their organization may be under an attempted attack based on customizable thresholds and notification methods.
Respond
Set policies to enable, disable, or create Application Control, Storage Control, or Network Control policies in response to specified observations.
Custom thresholds
Policies can be tailored to alert and respond differently based on the threat level to reduce alert fatigue.
Leverage knowledge
IT admins can easily share their own ThreatLocker Detect policies or “shop” for vetted policies shared by their industry peers and the ThreatLocker team.